I've been poking at AI coding agent internals for a while now, and honestly — the Claude Code source leak today hit different. Not because of the drama, but because it's the clearest window we've ever had into how a production-grade agentic coding tool actually works under the hood. Let me skip past the "oops" and get into what the architecture actually shows.
What Happened and Why (The Short Version)
Source Map in npm Package — What Went Wrong in the Build Pipeline
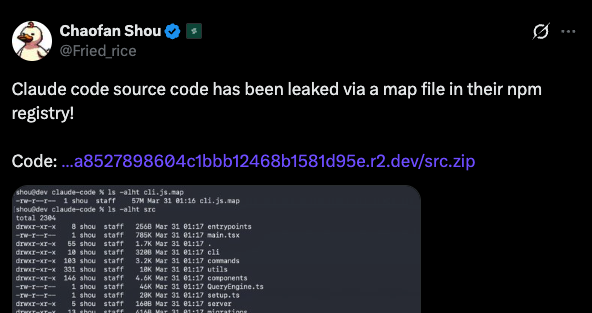
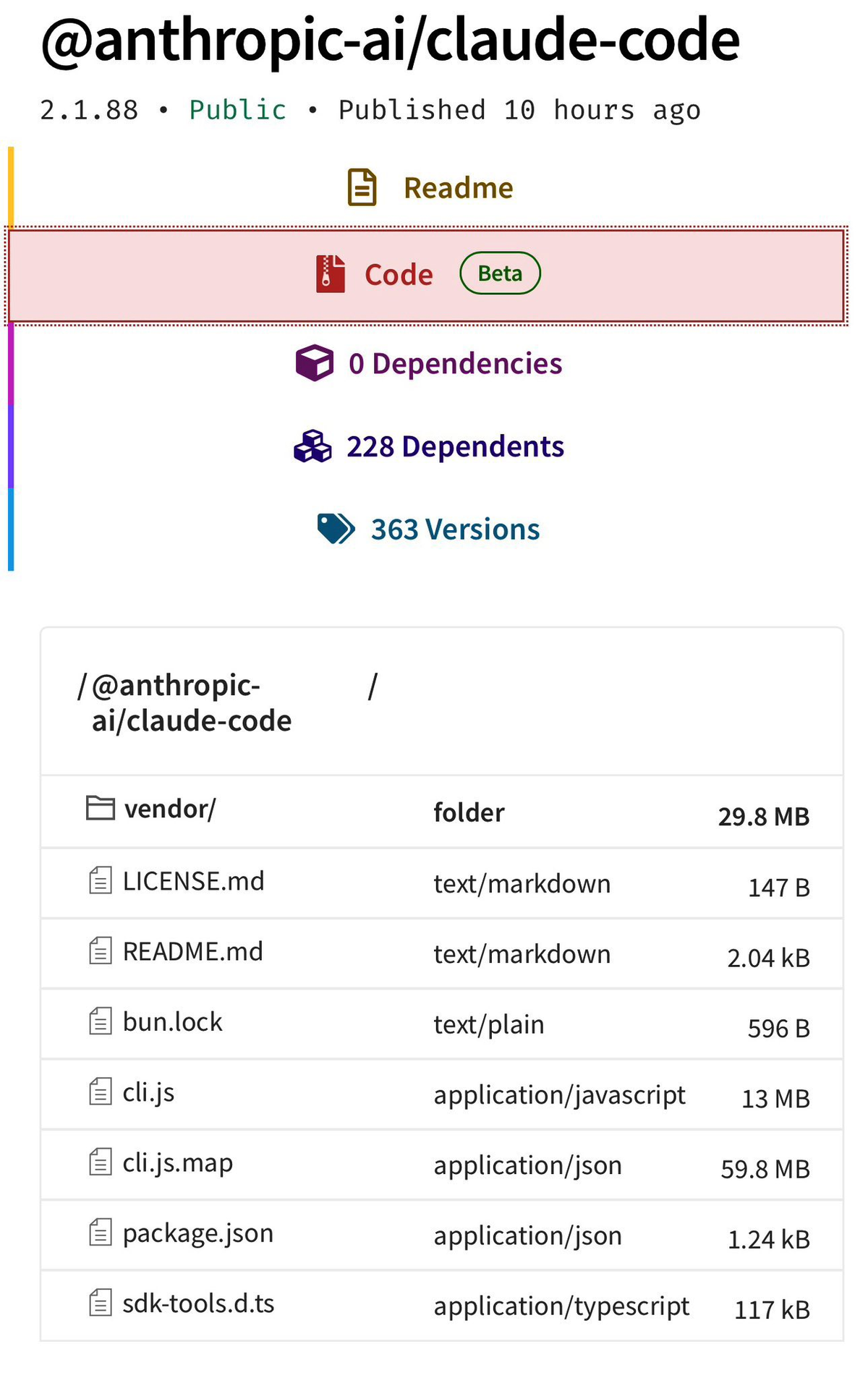
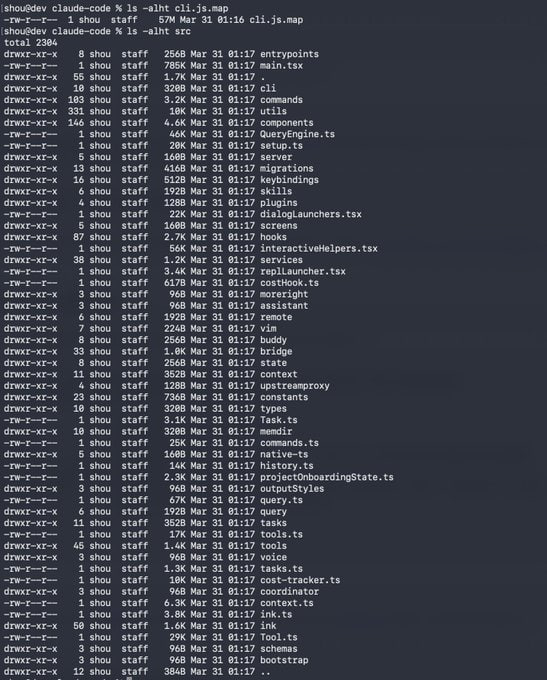
On March 31, 2026, security researcher Chaofan Shou spotted that version 2.1.88 of @anthropic-ai/claude-code on the npm registry had shipped with a 59.8 MB JavaScript source map file attached. A source map is a debugging artifact that maps minified production code back to its original readable source — enormously useful in development, catastrophic if shipped publicly.
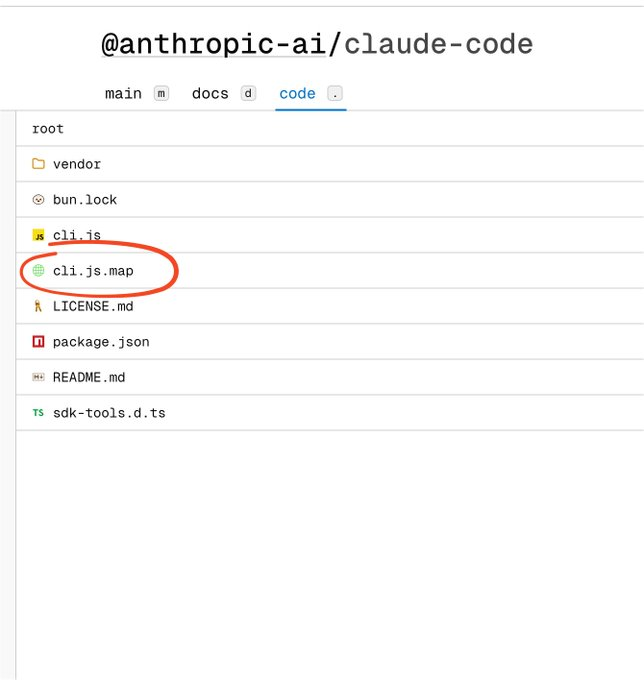
The map file pointed directly to a ZIP archive sitting on Anthropic's own Cloudflare R2 storage bucket. Nobody had to hack anything. Within hours, developers had downloaded and mirrored the complete, unobfuscated TypeScript codebase — 1,906 files, 512,000+ lines — across GitHub. The root cause: Claude Code uses the Bun runtime, which generates source maps by default. A missing *.map entry in .npmignore (or a missing sourceMap: false flag in the build config) was enough.
What Anthropic Confirmed (No User Data, Human Error, Second Incident in 13 Months)
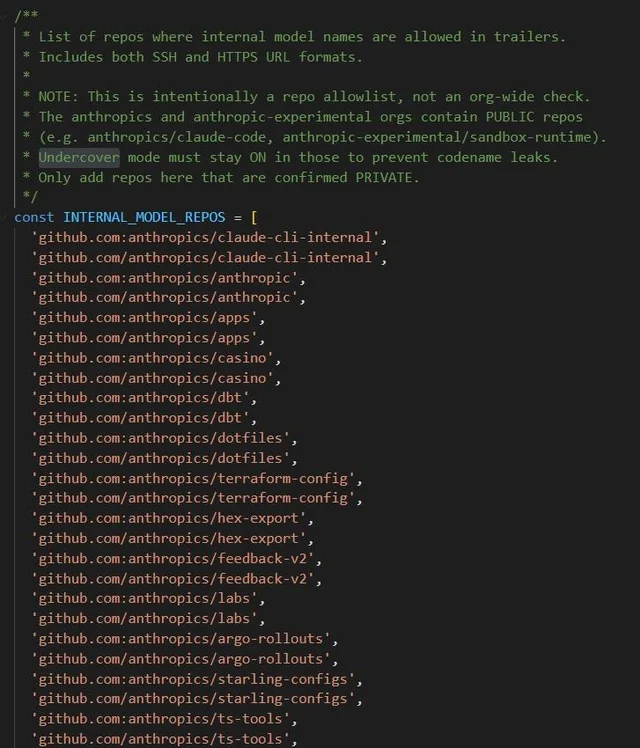
Anthropic confirmed to both The Register and VentureBeat: no customer data, no API keys, no model weights were exposed. "This was a release packaging issue caused by human error, not a security breach. We're rolling out measures to prevent this from happening again."
Worth noting: this is the second such incident. A nearly identical source-map leak occurred with an earlier Claude Code version in February 2025 — confirmed by multiple outlets in their reporting on today's incident. That one was patched. The recurrence is the more interesting signal for engineering teams than the leak itself. Separately, on the same morning, a supply-chain attack compromised the axios npm package (v1.14.1 and v0.30.4) with a Remote Access Trojan. That is an entirely unrelated incident — different attack vector, different package — but if you installed or updated Claude Code via npm between 00:21 and 03:29 UTC on March 31, audit your lockfiles for those axios versions.
What the Source Code Actually Contains
The Tool System: 40+ Permission-Gated Capabilities
The codebase is built around a discrete, permission-gated tool architecture. Each capability — file read, file write, Bash execution, web fetch, LSP integration, MCP server calls — is a standalone tool module. The base Tool.ts definition runs to roughly 29,000 lines of TypeScript. Every tool carries explicit permission requirements; the agent cannot execute a capability it hasn't been granted.
This is deliberate security architecture, not an afterthought. Each tool's permission gate is checked before execution, and the user approval flow is baked into the tool layer itself rather than handled by the LLM. That separation matters: the model decides what to attempt, but the tool system decides what is permitted.
The Query Engine: LLM Orchestration, Streaming, Caching
The largest single module is QueryEngine.ts at approximately 46,000 lines. This handles everything that touches the Anthropic API: prompt construction, streaming response handling, token counting, cost tracking, prompt caching, and the retry logic that keeps long-running agent sessions stable. The feature flag list embedded in this module is itself a product roadmap — including prompt-caching-scope-2026-01-05, token-efficient-tools-2026-03-28, and task-budgets-2026-03-13, which appear to be already-shipped or near-shipped capabilities.
Memory and Telemetry Systems
The memory architecture uses a three-layer pattern:
| Layer | Storage | Loading Strategy |
|---|---|---|
| Working context | MEMORY.md (lightweight) | Always loaded |
| Project notes | Separate structured files | On-demand |
| Session history | Past conversation logs | Selective search |
This tiered approach is how the agent maintains relevant context across long sessions without blowing the context window on everything it has ever seen. The telemetry system is more limited than the more alarming takes online suggest: it scans prompts for profanity as a frustration signal and tracks usage patterns, but does not log full user conversations or code content.
The Multi-Agent Architecture Patterns Worth Understanding
How Claude Code Handles Agent Spawning and Isolation
The orchestration model that emerges from the source is a lead-agent-plus-subagents pattern. A primary Claude instance coordinates the session, assigns subtasks, and spawns isolated subagents for parallel or context-isolated work. Each subagent runs in its own context window with a restricted tool set defined at spawn time. The subagent completes its task and returns only its output — not its full working context — to the orchestrator.
This isolation is intentional: exploratory or risky work stays out of the main context, and parallel workstreams don't contaminate each other's state. Tools implementing similar permission-gated multi-agent execution patterns — like Verdent's parallel worktree approach — reflect the same underlying engineering reasoning.
Permission Gates and How Approval Flows Are Structured
The approval flow architecture separates three distinct layers:
- Trust establishment — happens at project load time, before any tool execution
- Permission check — each tool validates its required permissions before running
- User confirmation — high-risk operations (file writes, Bash commands) surface an explicit approval prompt
The order matters. CVE-2025-59828 (patched earlier in 2025) was a vulnerability where Yarn-related code could execute before directory trust had been accepted — exactly the kind of pre-trust initialization issue that this architecture is designed to prevent. The source makes clear that trust sequencing is treated as a first-class correctness concern.
Why the Bash Tool Is the Real Orchestration Backbone
The Bash tool is architecturally central in a way that isn't obvious from the outside. It's not just a "run commands" capability — it's the primary mechanism through which the agent interacts with the host environment: running test suites, invoking build systems, executing git operations, and validating that its own code changes work. The validation loop — write code, run tests via Bash, check output, iterate — is the production reliability mechanism. Without a robust, permission-gated Bash tool, the agent's self-correction loop breaks down.
Feature Flags and What's Coming
What Confirmed Unshipped Features Suggest About the Roadmap
The codebase contains a feature flag registry with dozens of entries, a subset of which are compiled to false in the external build, indicating built-but-unshipped functionality. Based on what VentureBeat and other outlets confirmed from the code, the notable flagged items include:
afk-mode— Agent continues operating during user absenceadvisor-tool— An additional reasoning or planning layerredact-thinking— Ability to hide extended thinking traces from output- Browser automation via Playwright — Referenced in integration tests and flag configs
Anthropic had not officially announced these features as of the time of this writing. Treat them as confirmed-in-development, not confirmed-shipping.
KAIROS Background Daemon — Always-On Agent Pattern
KAIROS is the most architecturally significant unshipped item in the leak. Per reporting across multiple outlets, it describes a daemon mode in which Claude Code operates as a persistent background agent rather than a prompt-and-response loop. The associated autoDream process handles memory consolidation during idle periods — merging observations, resolving contradictions, promoting tentative notes to verified facts — without interrupting the active session context.
This is the always-on agent pattern: instead of the user's workflow being blocked while the agent thinks, the agent continues background work asynchronously. The implementation uses a forked subagent specifically to prevent the main agent's context from being corrupted by its own maintenance routines. That's mature engineering.
The Build Pipeline Lesson (For Any Engineering Team)
Why Bun Generates Source Maps by Default
Bun's bundler defaults to sourcemap: "linked" in development configurations. In production builds, this needs to be explicitly overridden. The same issue applies to esbuild (which Bun wraps) and several other modern bundlers. "It worked in CI" doesn't catch this if your CI environment mirrors your dev config.
npm Publish Checklist Every Team Should Run
This is the part worth saving. The following checklist would have caught Anthropic's mistake at step 2:
# 1. Dry-run before every publish — inspect exactly what ships
npm publish --dry-run
# 2. Audit the file list explicitly — look for anything unexpected
npm pack --dry-run 2>&1 | grep -E "\.(map|env|key|pem|secret)$"
# 3. Confirm your .npmignore or package.json "files" field is correct
# .npmignore should include:
# *.map
# *.map.js
# **/*.map
# src/ (if you only ship dist/)
# 4. Validate the packaged tarball directly
npm pack
tar -tzf *.tgz | grep "\.map$" # should return nothing
# 5. Run a post-pack diff against your expected file list
tar -tzf *.tgz > actual-files.txt
diff expected-files.txt actual-files.txtFor teams using Bun specifically, add sourceMap: false (or sourceMap: "none") to your production build config explicitly — do not rely on the default being safe:
// bunbuild.config.ts — production build
await Bun.build({
entrypoints: ["./src/index.ts"],
outdir: "./dist",
sourcemap: "none", // ← explicit, not assumed
minify: true,
});Add a prepublishOnly script to package.json as a last-resort gate:
{
"scripts": {
"prepublishOnly": "node -e \"const fs=require('fs');const files=require('./package.json').files||[];if(!files.length)process.exit(0);\" && npm pack --dry-run 2>&1 | grep -q '\\.map$' && echo 'ERROR: .map files detected in package' && exit 1 || exit 0"
}
}FAQ
Was Any User Data or API Key Exposed?
No. Anthropic confirmed explicitly: no customer data, no credentials, no model weights, no inference infrastructure were involved. What leaked was Anthropic's own proprietary source code — an intellectual property exposure, not a user data breach.
Is It Safe to Keep Using Claude Code?
Yes, with one caveat. The source code exposure itself does not put users at risk. However, if you installed or updated Claude Code via npm on March 31, 2026 between 00:21 and 03:29 UTC, you should check your lockfiles for the compromised axios versions (1.14.1 or 0.30.4) — that is an unrelated supply-chain attack that coincidentally occurred in the same window. Rotate API keys as a precaution if you were in that window.
Should Teams on npm Migrate to the Native Installer?
Yes. Anthropic has designated the native installer as the recommended installation method going forward. It ships as a standalone binary that bypasses the npm dependency chain entirely, eliminating npm supply-chain exposure as a risk surface. It also supports background auto-updates. If you must remain on npm, pin to version 2.1.86 or earlier (confirmed clean) until Anthropic publishes a verified clean release.
What's the Difference Between This and the February 2025 Incident?
The February 2025 incident was a nearly identical packaging error — a source map file shipped in an early Claude Code npm package, confirmed by The Register as part of their reporting on today's recurrence. That version was pulled and patched. The March 2026 incident is the same class of error, different version, much larger codebase. The February 2025 incident did not receive the same level of attention because Claude Code was less widely deployed at the time. Do not conflate either of these with the separate March 26, 2026 CMS configuration error that exposed draft blog content about unreleased models — three separate incidents, three separate misconfiguration types, all within roughly a week of each other.
Related Reading
- Claude Code vs Verdent: Multi-Agent Architecture Compared
- Best Claude Code Alternatives for Agentic Workflows in 2026
- Claude Code Pricing 2026: Plans, Token Costs, and Real Usage Estimates
- Claude Skills vs MCP vs Agents: Key Differences
- What Is Model Context Protocol?
All references to leaked source code in this article are based on publicly available analysis from The Register, VentureBeat, and other reporting, and on descriptions of the code rather than reproduction of it. No proprietary source code is quoted or reproduced here.
